March 9, 2026
Hopp
Cybersecurity
For years, cybersecurity strategies were built around a clear assumption: protect the network perimeter. Firewalls, VPNs, and internal network segmentation formed the strongest line of defense. If you were inside the corporate network, you were trusted
Modern organizations operate in hybrid environments. Users connect from home networks, mobile devices, cloud platforms, and SaaS applications. The concept of a clearly defined internal network has faded. The concept of a clearly defined internal boundary has faded. There is no automatic security in simply being connected to the corporate environment.
Access today is granted based on identity – not location.
The perimeter hasn’t disappeared. It has shifted.
Cyberattacks have changed dramatically over the past decade.
In the past, attackers focused on exploiting software vulnerabilities, deploying malware, or breaching systems through technical weaknesses. The objective was clear: force unauthorized access.
Today, attackers have adopted a more subtle and effective approach. Instead of forcing entry, they target user identities. Through phishing, credential theft, or token compromise, they obtain valid credentials. Once authenticated, they operate as legitimate users – often without triggering immediate suspicion.
This shift is critical. Malicious activity often appears normal. When valid credentials are used, traditional defenses may detect nothing unusual. From the system’s perspective, it is simply another successful login.
The strategy has changed. Attackers no longer need to break in – they log in and blend in.
One stolen account can open the door to everything you thought was secure.
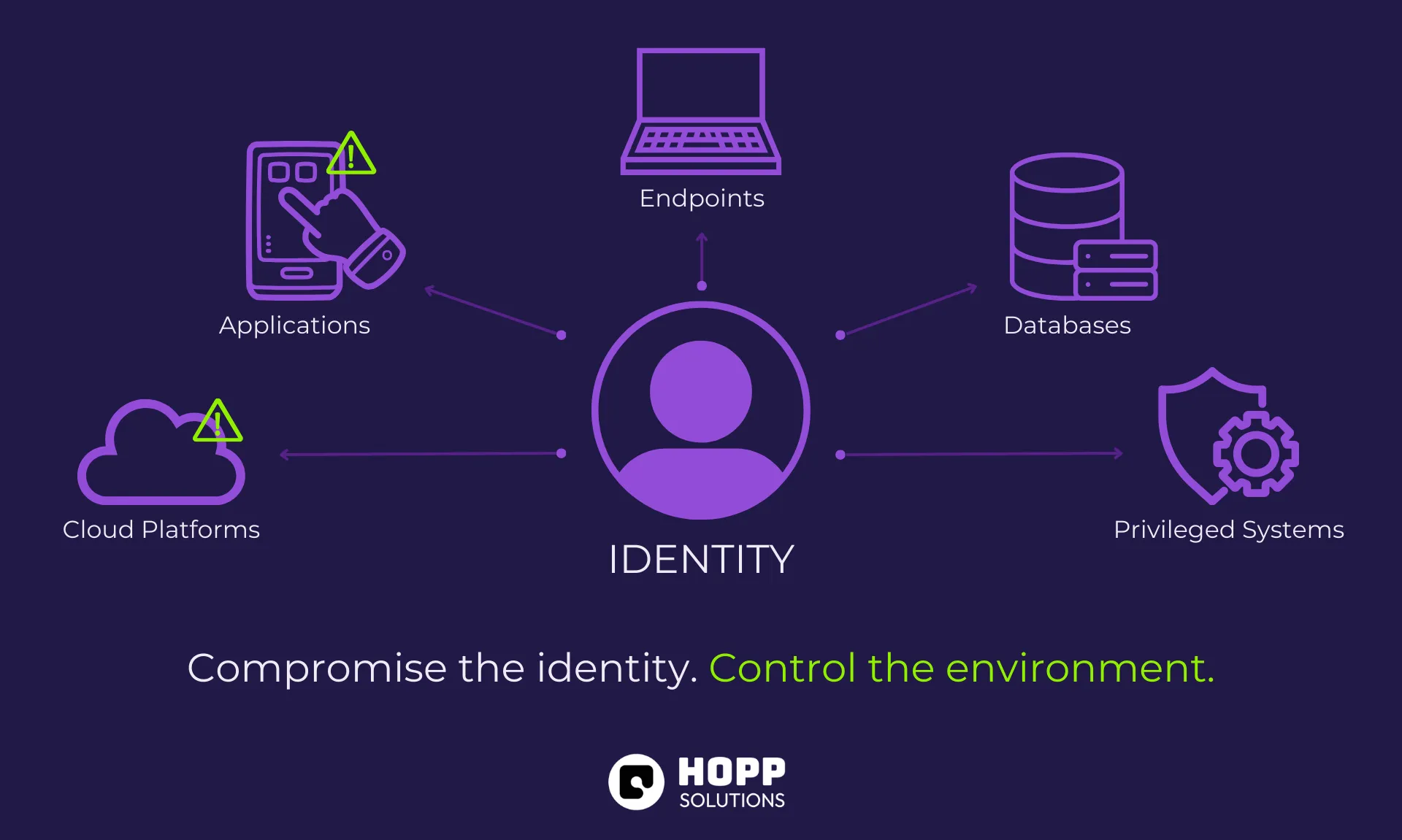
A single compromised account can provide access to multiple systems, cloud services, applications, and sensitive data. In many environments, accounts hold more permissions than necessary – and attackers know how to take advantage of that.
Take control of a privileged account, and the consequences escalate quickly:
When an identity is compromised, everything connected to it becomes vulnerable. Identity is not just a credential; it is the gateway to your entire organization.
Microsoft Defender for Identity shifts the focus from detecting known threats to understanding how identities behave.
Instead of relying only on predefined attack signatures, it continuously monitors authentication activity to establish what “normal” looks like within an organization. When behavior deviates from that baseline – unusual login patterns, unexpected privilege use, abnormal access behavior – alerts are triggered before damage escalates.
By focusing on behavior rather than static rules, it detects threats that blend into legitimate activity – precisely where traditional perimeter defenses often fail.
Initially, I believed endpoint protection was the strongest layer of defense. Securing devices against malware and vulnerabilities felt like the foundation of security.
But understanding identity-based attacks changed that perspective.
These attacks rarely trigger obvious alarms. There is no visible breach or system crash. Instead, there are subtle indicators – a login at an unusual time, unexpected resource access, a small change in privilege usage. Individually they seem insignificant. Together, they can signal something far more serious.
Security is no longer just about protecting devices. It is about recognizing behavioral patterns before they become incidents.
Identity security cannot be treated as a secondary control layer. It must be embedded into overall security strategy.
Modern security frameworks such as Zero Trust emphasize continuous verification. Trust is not granted simply because credentials are valid. Authentication and authorization must be evaluated continuously based on context, behavior, and risk.
Strategic identity protection in includes:
In cloud-connected infrastructures, identity links endpoints, applications, and data. Protecting it strengthens the entire ecosystem.
Identity monitoring is not just about preventing breaches – it is about reducing risk exposure and improving organizational resilience.
Cybersecurity has fundamentally shifted. The boundary that once surrounded the network, now surrounds identity.
When access decisions are based on who someone is rather than where they connect from, identity becomes the true control point.
Protect it – and you protect everything connected to it.
Designing and developing digital experiences that move businesses forward.
Contact
hello@hoppsolutions.com
+49 155 1027 5723
+389 77 540 743
Office
ul. Nikola Karev br. TC. TR
6000 Ohrid, North Macedonia
Made with love by Hopp Solutions | 2026